Share via
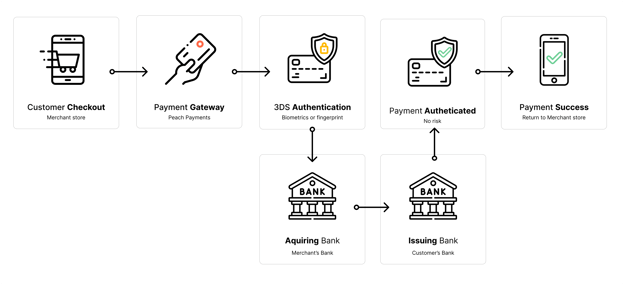
3D secure is a security protocol that adds a layer of authentication to the online payment experience by verifying a cardholder’s identity when they are using their card details instead of swiping with their actual card. The purpose is to protect a customer’s card against unauthorised use when shopping online.
The first iteration of 3DS appeared in 1999. Card networks like Visa (Verified by Visa) and Mastercard (Mastercard Identity Check) implemented this feature in 2001. In the first iteration, customers needed to authenticate themselves using OTP or One Time Password.
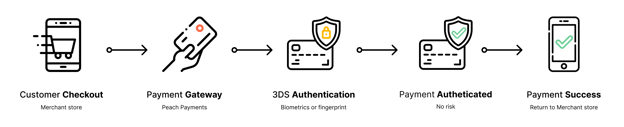
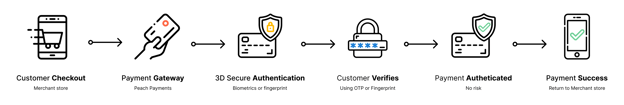
To authenticate the customer is usually required to provide something they have (device), something you know (One Time Pin), or something you are (Biometrics – like a fingerprint)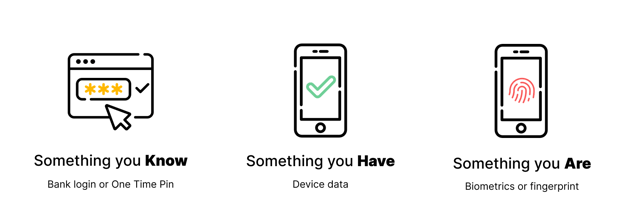
3DS involves three domains: the acquiring bank (or the merchant’s bank), the issuing bank (or the cardholder’s bank), and the infrastructure supporting this protocol, such as Peach Payments.
3DS 1.0 promised to help prevent fraud by shifting the burden of authentication onto the issuers (Customer’s bank). This led to a huge loss in false declines as customers would choose to cancel a transaction when seeing a 3DS pop-up (or more likely a redirect) to avoid any potential fraud.
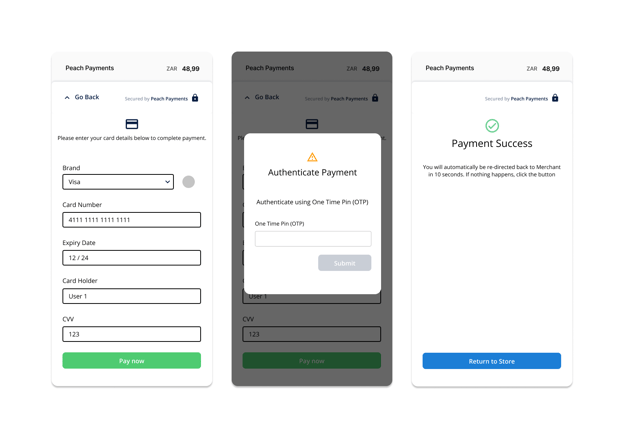
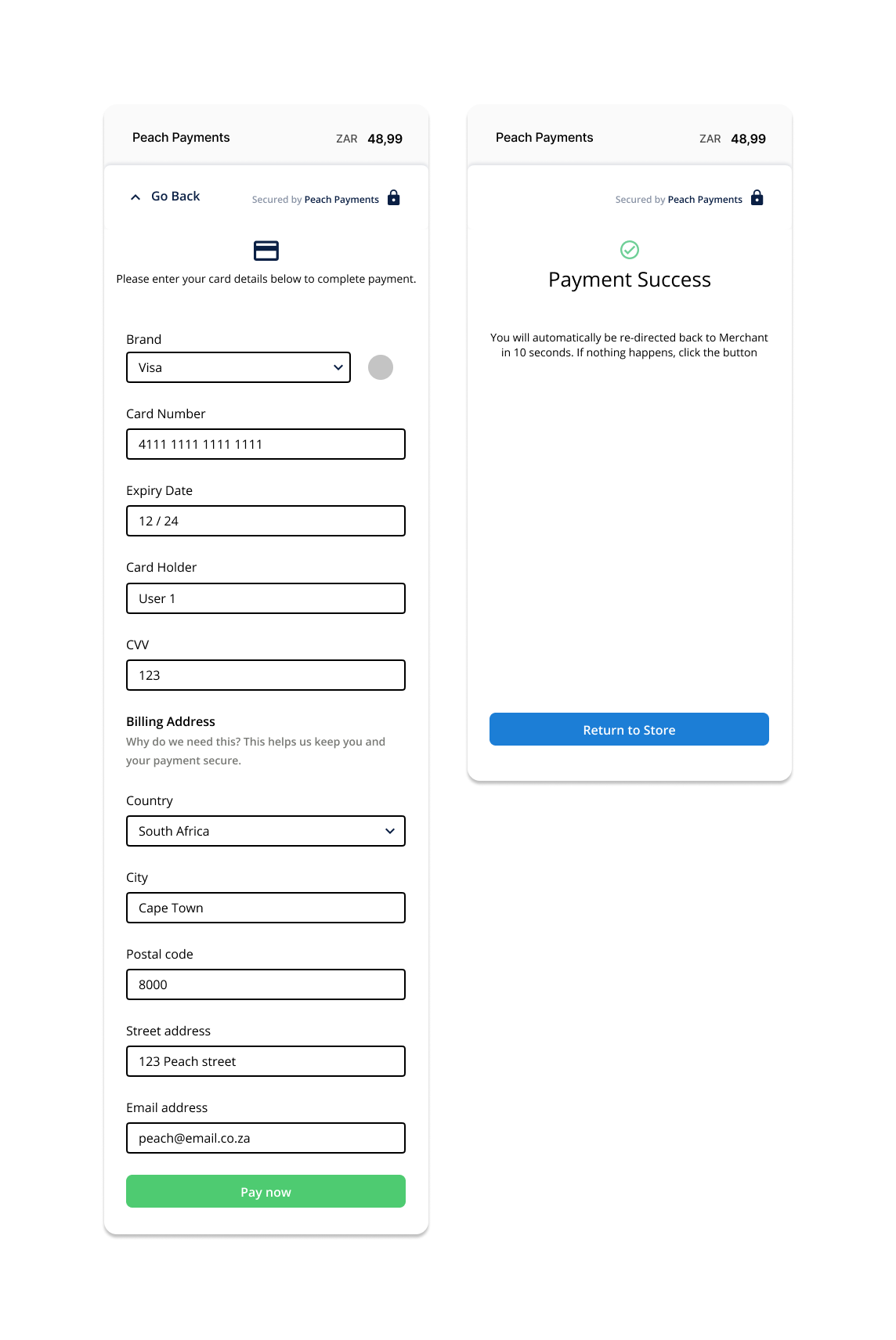
So what does 3DS look like?
You know when you buy something online and a little pop up appears asking you to enter an OTP or approve your purchase in your banking app? Yup, that’s 3DSecure in action.
What improvements are found in 3D Secure 2.0?
3DS 2.0 offers additional fraud protection by analysing information about the customer and prompting them to verify their identity when making a high risk transaction. By assessing the customer’s information and the risk of their transaction, customer’s may not have to verify their identity to authenticate every transaction they make.
What does it look like? No extra steps, no pop ups and no OTP or fingerprint needed!
When a transaction is trusted the customer will continue on the frictionless flow (No OTP or Biometrics required to authenticate)
If a transaction is deemed suspicious or high-risk, the customer is then required to authenticate (OTP or Biometrics) in the challenge flow.
What is risk-based authentication?
Risk-based authentication is the process of determining the risk attached to a particular transaction and, based on that risk level, whether or not the customer should be challenged.
The risk-based assessment includes:
- The value of the transaction
- New or existing customer
- Transactional history
- Behavioural history
- Device information
- Shipping Address
- Billing Address
What does this mean for Peach Merchants?
Peach Merchants are not required to make any changes, although they do have the option to submit additional data related to customers and transactions to further improve their customer’s online purchasing experience.
So should you? It has been shown that 3DS 2.0 can increase conversion rates by almost 8%, reduce false declines and is overall a better checkout experience.
Additional data points:
- Account Type
- Address Match Indicator
- Browser IP Address
- Cardholder Billing Address
- Cardholder Email Address
- Cardholder Home, Mobile, Work Phone Number
- Cardholder Name
- 3DS Requestor Non-payment Indicator
- Cardholder Shipping Address
- DS Reference Number
- EMV Payment Token Indicator
- SDK Encrypted Data
- Transaction Type
- 3DS Requestor Challenge Indicator
- 3DS Server Operator ID
- Cardholder Account Identifier
Conclusion
Peach Payments will be supporting 3DS 2.0 by 31st October 2021 and will be expecting all Merchants to support 3DS 2.0 by 31st October 2022 as 3DS 1.0 will no longer be supported by our banks.
Peach Payments is always looking to improve our product and customer experience. 3DS 2.0 is the next step in fraud prevention and a big leap in improving the customer online purchasing experience, and upping your business’s conversion rate.
Scale with Peach
Learn how we help scale some of Africa's most exciting businesses
Business tips, case studies, interviews with online store owners and business trends…
The New Standard for Payouts in South Africa

Peach Payments and Yoyo add bank card-linked loyalty to Digit Pro POS device
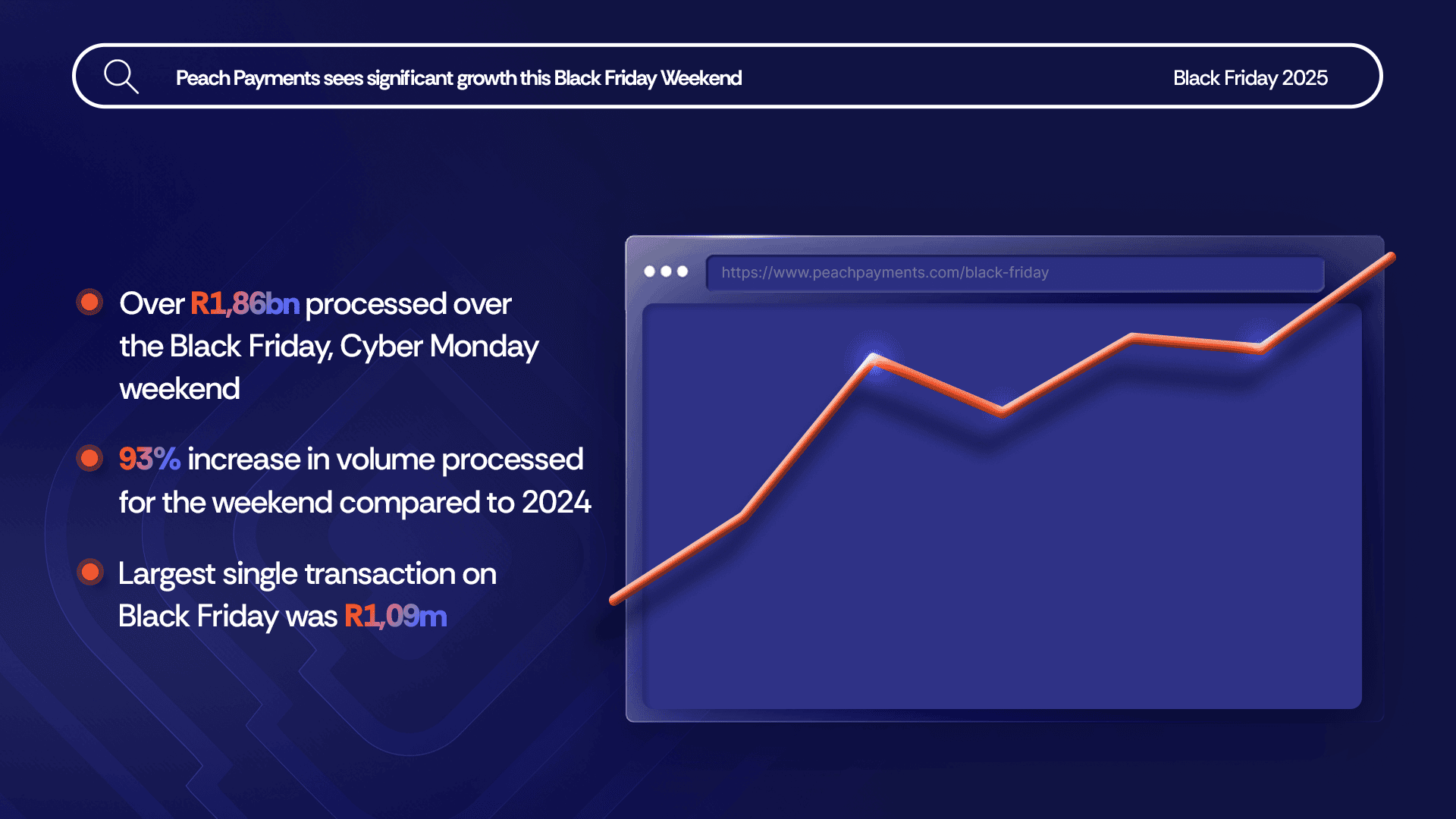
Black Friday up 93% over 2024, R1,86bn processed

Bringing Our New Peach Values to Life

Samsonite in-store payment methods
How global and regional companies can use the Mauritius IFC to centralise online payments and treasury functions

# PeachFriday Merchant Deals 2025

A merchant’s guide to chargebacks
Four Black Friday payment realities for merchants

What are Direct Merchant Accounts (ISO) versus Aggregation Accounts?

What Is 3RI? Everthing you need to know about Requestor-Initiated Authentication

Highlights from the 2025 World Wide Worx Online Retail Report

What is Interchange? Everything you need to know about interchange fees
Cadana Pay x Peach Payments: Unlocking seamless global Payouts
Peach Payments announces real-time clearance Payouts
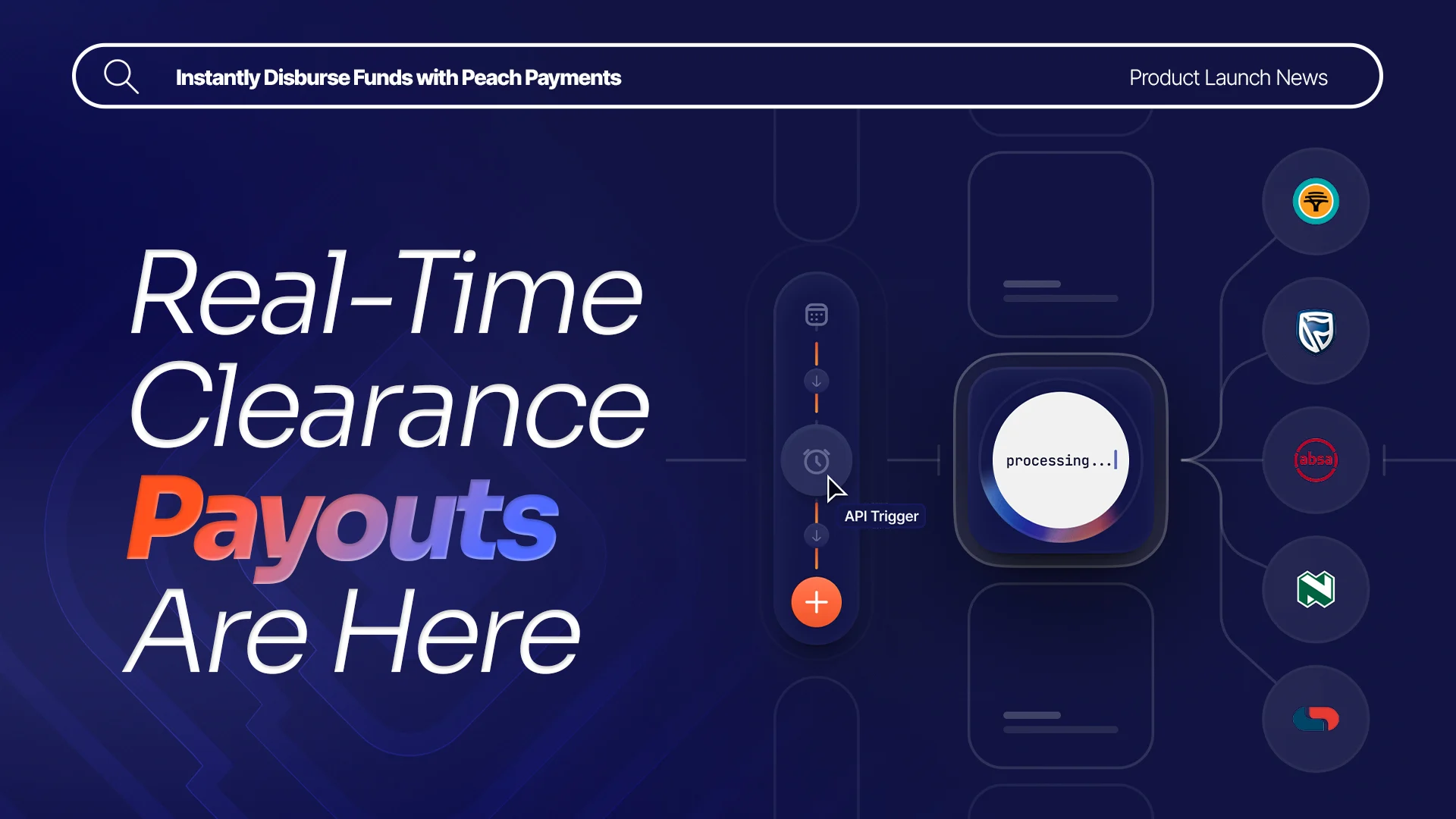
Peach Payments x MoneyBadger partnership goes live

Peach Payments launches enterprise-level POS terminal

iTickets x Peach Payments Point of Sale

Peach Payments x Digicape: Powering Premium Apple Experiences with Seamless Payments

Peach Payments acquires West-African payments gateway PayDunya
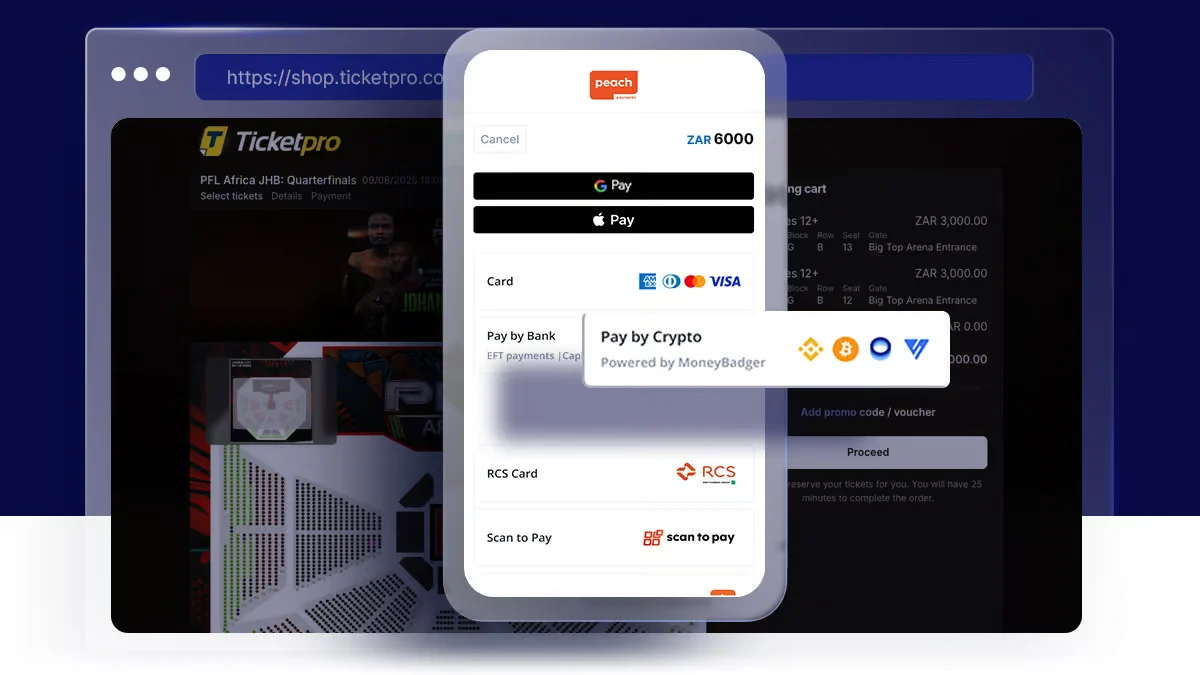
Navigating International Transactions
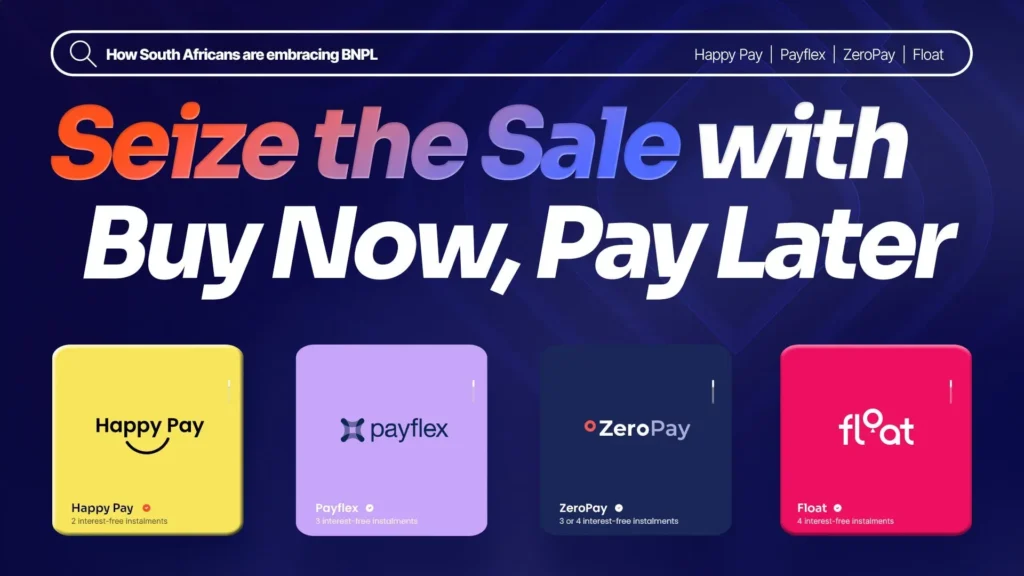
Seize the Sale with Buy Now, Pay Later

2024 Wrapped: A Year of Innovation and Growth at Peach Payments
RCS payment option now available through Peach Payments

Peach Payments sees impressive growth this Black Friday Weekend

#PeachFriday Merchant Deals 2024
Your Ultimate Guide to Payment Security for Black Friday

Scaling with Peach Payments: Unveiling the Product Roadmap

Scaling with Peach Payments: Revolutionising Reconciliation

Scaling with Peach Payments: The Future of Payments